Smile, you’re ̶o̶n̶ ̶c̶a̶m̶e̶r̶a̶ being listened to: side-channel attacks
Rédigé par Célestin Hernandez
-
30 April 2026With a rather disconcerting counterintuitiveness, SCAs (Side Channel Attacks) are capable of inferring data by exploiting information that may at first glance seem completely unrelated. The LINC offers here an overview of these attacks.

What is an SCA?
A first definition
If the title of this article made you raise an eyebrow, that’s an excellent start. The choice of words, although an obvious reference to… something not entirely clear, mainly serves as an introduction to what could constitute a side-channel attack: detecting, solely through sound, the facial expressions of a person while they are speaking.
If this first example still isn’t clear enough, here’s a second one, also rooted in popular culture: in movies, it’s common to see thieves and spies open safes using only the sound of their mechanisms; this is a proper side-channel attack. Indeed, if we follow a generic definition: it consists of collecting, interpreting, and exploiting signals emitted (involuntarily - think of it as a leak) during the operation of a system in order to deduce secrets (passwords or private data). In the case of the safe and its mechanisms, a rogue who knows how to interpret these sounds can sometimes guess the combination. They are therefore collecting and exploiting a signal emitted by the locking system to deduce the combination (a clever rogue indeed).
However, side-channel attacks are not limited to simple auditory channels or acoustic measurements. In today’s digital age, there is no shortage of physical or numerical measurements of how a system operates, and these can sometimes reveal secrets one would have preferred to keep hidden. These measurements are often correlated (for example, the intensity of a system’s electric current is intrinsically linked to the magnetic field it generates), thereby making the attack surface at least twice as large, as we will see later.
The birth of SCAs
If the safe example reinforces the idea that side-channel attacks are not a recent phenomenon, this is also true for those that are of particular interest in this article. It is generally accepted that one of the first theorized or documented attacks was identified by Paul C. Kocher in 1996, in his publication Timing Attacks on Implementations of Diffie-Hellman, RSA, DSS, and Other Systems.
(Editor’s note: it should be noted that the attack introduced by Paul Kocher is not necessarily the very first ever to have existed. In fact, as early as the Second World War, initial work carried out by Bell Labs pointed to the possibility of intercepting communications on battlefields through the analysis of electromagnetic signals. These findings were classified, but part of the scientific community was already aware of these risks. It considered that the feasibility of such attacks was limited to entities with enormous resources, such as governments, and did not immediately engage with the topic. However, in 1985, Wim van Eck published the first declassified technical analysis demonstrating that such attacks were entirely within reach of ordinary individuals (the equipment used costing less than $20). These attacks are not strictly speaking side-channel attacks and are more closely related to covert eavesdropping (the boundary is admittedly thin, but the distinction is important)).
In this publication, Kocher sought to draw the scientific community’s attention to the risk that the execution time of cryptographic operations using a private key could potentially reveal the private key itself.
For non-cryptologists and novice computer scientists, let’s try to simplify things:
- The attack presented by Kocher works on encryption protocols used for cryptographic key exchange, including Diffie–Hellman and RSA.
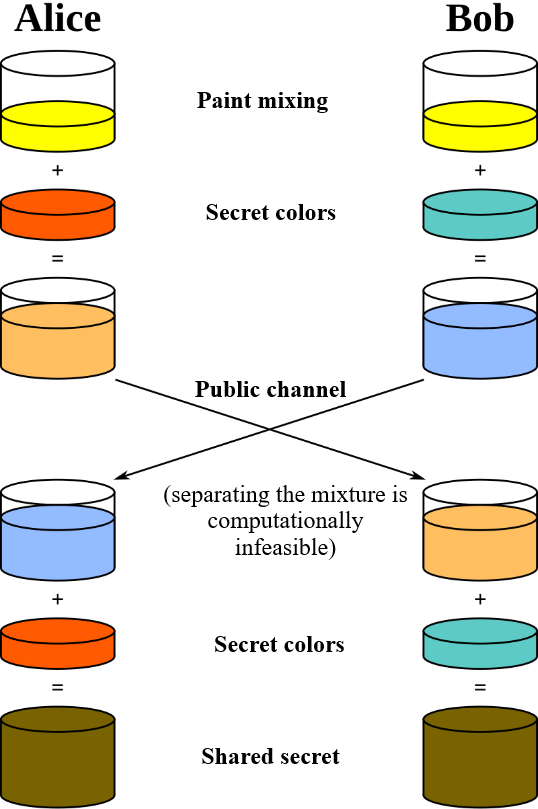
- Without going into the details of each of these protocols, let’s at least simplify one of them: Diffie–Hellman (the mathematical operations are not crucial, the principle is what matters!):
- Let’s call the two parties wishing to communicate, as tradition dictates: Alice and Bob.
- Alice and Bob want to communicate over a potentially monitored communication channel. To keep their communications confidential, they must agree on a shared secret: a key that would allow them, and only them, to encrypt and decrypt their messages.
- However, they cannot communicate this secret directly (it may be intercepted), so they agree on two public values: p and g (which they exchange).
- Alice then chooses a secret a, and Bob a secret b (which they do not share).
- Alice calculates (don’t try to do it for her) : A=gamod p and Bob : B=gbmod p. They then publicly exchange A and B.
- Alice then calculates: K=Bamod p and Bob : K'=Abmod p. Thanks to a mathematical property (exponential commutativity, if you insist), we have: K=K'=gabmod p.
- K is therefore the shared secret, and neither Alice nor Bob has transmitted it in cleartext. They can now use this secret to encrypt and decrypt their communications. The key point is that even if an attacker knows all of p, g, A, B, and the other publicly exchanged communications, it is extremely costly, if not practically impossible, for them to recover Alice’s or Bob’s secrets a or b. The mathematical operation used to compute A, B, and K is very ‘easy’ to perform computationally, but vastly more difficult to ‘invert’ (if you’ve made it this far, it is no insult to say that this is the discrete logarithm problem).
- Now, to understand the attack:
- As we mentioned earlier, the attacker already knows p, g, A, and B. To reconstruct the shared secret between Alice and Bob, they only need to recover either Alice’s private key (a) or Bob’s private key (b). Indeed, if they manage to recover a, they can calculate K = Bamod p (and conversely for b), and thus decrypt all communications between Bob and Alice.
- To do this, the attacker will need to arm themselves with patience and send Bob a large number of (different) values of g so that Bob calculates B = gbmod p many times. With each new calculation, the attacker will precisely measure the time it takes Bob to respond. But what can they possibly do with simple execution time measurements?
- To put it simply and quickly, the algorithm used to calculate B (the modular exponentiation operation) sometimes uses « branches » to improve computational efficiency. These programmatic branches depend on the bits of the exponent: the secret key. If the bit is 0, the operation consists only of a squaring, whereas if the bit is 1, the operation additionally includes a multiplication (we will stick to this level of detail). Thus, depending on whether the bit is 0 or 1, the calculation time will differ noticeably.
- Since the attacker knows all the values that were sent, by being statistically clever they can deduce the bits of the exponent one by one, and eventually fully recover the secret.
Congratulations, if you’ve made it to the end of this part, you’ve understood the basic idea behind the first theorized side-channel attack.
However, although quite remarkable on paper, this attack received mixed feelings from the scientific community at the time; while it acknowledged the major conceptual breakthrough, it could not help but point out a few limitations (as you may have done yourself).
Indeed, the attack notably does not work if:
- The implementation of the mathematical operations does not use branching (i.e., if it runs in constant time);
- The private keys change depending on the interlocutor;
- The attacker does not have sufficient resolution or suitable conditions to accurately measure time (which is the case in « real » systems, where they will face noise, system-induced latencies such as other processes, etc.);
- The attacker cannot interact with their target (which is sometimes the case in secured environments).
Although this did not call into question the seriousness or the potential of Kocher’s findings, a large number of engineers downplayed their practical impact. The risk was real, but its likelihood was considered far too low.
A proof by example and attacks that had concrete impacts
Despite these reservations, Paul Kocher did not back down. He persisted and published a second paper in 1999 :Differential Power Analysis, in which he highlighted another way to recover secret keys: power consumption analysis (the principle is essentially the same as the previously introduced attack, but this time it is the power consumption during computation that enables bit-by-bit inference). This demonstration strongly raised awareness within the scientific community, which no longer saw Paul Kocher’s proposals as a mere artifact or anecdotal discovery, but as a clearly identified risk whose various facets were crucial to explore in full.
Thus, the 2000s saw a sharp increase in publications related to side-channel attacks. In 2003, the paper Remote Timing Attacks are Practical finally demonstrated the feasibility of the timing attacks proposed by Paul Kocher (the paper shows that measurements can be taken « remotely » and that they are fairly resilient to noise).
We will have the opportunity later to discuss the variability and creativity of the channels chosen by attackers, but it is important to understand that this field of research (even if it may, despite the early examples, seem exotic or even far-fetched) has had considerable direct and indirect impacts on the industry. As the first editorial note mentioned, the United States had already become aware during the Second World War of the risks of secrets leaking through the analysis of electromagnetic signals. These risks were limited to those of simple covert interception, rather than side-channel attacks. Nevertheless, NATO and the NSA continued to expand their research efforts in order to establish a common standard: TEMPEST, which defines security measures to mitigate the impact of such leaks and does in fact take side-channel channels into account.
Another significant impact of side-channel attacks is related to the Spectre / Meltdown vulnerabilities.
- Meltdown: this hardware vulnerability discovered in 2018 exploits (like the first attack by Paul Kocher) a programmatic ‘branching’ mechanism used to improve execution time, and infers confidential information from timing variations (similar to the bit-by-bit comparison you have, of course, perfectly understood). To better understand it, what would seem logical (at least to an untrained eye) is that when an application tries to access data stored in memory, the processor must first check whether that application is allowed to read that memory (are you following?). However, some Intel processors use what is known as speculative execution: before even verifying whether the application has permission to read the memory, the processor accesses it anyway (in order to save time), and only checks the application’s privileges afterwards. By statistically varying (as in the bit-by-bit attack) memory read requests and measuring the delay before access denial is returned, a malicious actor can gradually infer what is stored in a memory area they are not authorized to access.
- Spectre : this covers an entire class of vulnerabilities similar to the one introduced by Meltdown. In summary, Spectre exploits branch prediction: a process normally executes instructions sequentially (one after another) and keeps track of the set of instructions it will execute next. To save time, these instructions are sometimes executed in advance, and Spectre exploits this speculative execution (and its associated timing) to infer information that is supposed to remain secret. (The vulnerability is generally much more complex, but we will spare you yet another detailed description).
It is important to understand that, in 2018, these two vulnerabilities affected almost all computing systems (PCs, smartphones, tablets, and the like). As a result, mitigation costs were estimated to amount to several billion dollars (for replacing processors or carrying out updates and patching operations). In connection with these patching efforts, one solution sometimes adopted was to « remove » programmatic branching mechanisms, which had the effect of reducing the performance of certain applications (with an estimated performance drop of around 5 to 10% since this loss of performance was observed, investments to compensate for it were also significant).
Attacks whose diversity rivals their inventiveness
Two main families
Side-channel attacks are divided into two main families: invasive and non-invasive attacks. The notion of intrusiveness introduced here refers to the degree of access an attacker has to the system they wish to compromise, in a manner similar to the evaluation approaches used in black-box and white-box testing of computer systems. Black-box testing assumes a general lack of knowledge about the system, whereas white-box testing, on the contrary, assumes the complete absence of black boxes (the entire system and all its components are known and accessible).
A non-invasive side-channel attack will merely (like the rogue with the safe mentioned in the introduction) carry out a passive « listening » of the system: by analysing its power consumption, the execution time of a task, or the noise emitted by the system, for example (yes, the example remains relevant even in computing).
For invasive side-channel attacks, these no longer rely on simple passivity but actively seek to interact as much as possible with the hardware components of the system, even if this means damaging it (rather than measuring the system’s overall power consumption, one may, if access is available, measure the consumption of specific components).
However, it is difficult to map side-channel attacks in a straightforward manner. As mentioned in the introduction, they exploit the mathematical and physical relationships between all measurable properties of a system: time, power consumption, and electromagnetic fields. Moreover, attack surfaces are as diverse as they are unconventional, to the point that one may wonder, given the current state of research, what is not a side-channel attack!
With countless ramifications
To better grasp the ineffable nature of the ingenuity behind side-channel attacks, the LINC offers you an overview in the style of “SCA’s greatest hits.
The Visual Microphone: Passive Recovery of Sound from Video
In a 2014 paper, American researchers showed that it was possible to recover audio from a video without necessarily needing to read lips. To do so, they exploited the physical property inherent to sound: vibration. You may or may not be aware that an object producing sound vibrates; these vibrations propagate to our ears, but they can also affect surrounding objects and cause them to vibrate as well. By capturing these vibrations through the analysis of a high-speed video, the researchers demonstrated the possibility of recovering the sound heard in a room based on the vibrations of water, a plant (and, more difficultly, a brick). Video illustration here.
Acoustic Side‑Channel Attacks on a Computer Mouse, Acoustic Side Channel Attack on Keyboards Based on Typing Patterns and Hearing Your Touch: A New Acoustic Side Channel on Smartphones
The three research papers listed here use everyday objects from our digital lives: the mouse, the keyboard, and even the touchscreen of a smartphone. Based on the sounds emitted when these are used, the various research groups are able to reconstruct the position of a mouse on the screen, the sequence of characters typed on a keyboard, or the position of a finger on a smartphone screen. It is important to note that papers exploring these topics are relatively « old »; however, a strong resurgence of experimentation is currently being observed. Even though performance is still limited to environments where the attacker knows the hardware model and where ambient noise is low, the increasingly advanced capabilities of artificial intelligence are strengthening the potential for these attacks to generalize.
Optical Cryptanalysis : Recovering Cryptographic Keys from Power LED Light Fluctuations
This paper builds on the idea of the examples we mentioned in the introduction: recovering private keys to decrypt communications. Here, timing analysis, power consumption, and electromagnetic emissions are no longer the focus; instead, the researchers manage to infer cryptographic keys based on fluctuations in LED light (found in particular on laptops, where they are sometimes used as indicators for power, charging status, and so on).
Lest We Remember : Cold Boot Attacks on Encryption Keys
The authors exploit here a lesser-known channel: the persistence of the internal state of memory after power shutdown. To better understand this, it is important to know that a computer can retain data (including sensitive information) in its RAM for a few seconds or even several minutes after power is cut. To extend this retention time, the authors literally freeze the memory modules in order to provide enough time to exploit the residual data (and potentially recover encryption keys or other secrets).
For a more “technical” taxonomy proposal and a broader overview, see here. For a focus on power side-channel attacks, see the extensive study here.
In this article, the researchers exploit electromagnetic signals from an HDMI cable. As mentioned earlier, every electrical current induces an electromagnetic signal around the cable through which electrons flow (the right-hand rule). Using deep learning algorithms, it is possible to infer from this signal a degraded version of the image being transmitted through the HDMI cable and display it on a screen, allowing the TEMPEST attacker to monitor the victim’s screen in real time.
For a better understanding of this article, see here.
The challenges of accounting for SCA (Side-Channel Attacks)
As we hope to have sufficiently demonstrated, side-channel attacks exploit as many attack surfaces as can be imagined (sometimes going beyond comprehension). It is therefore legitimate to ask how to protect against them.
More complex (without any value judgment) than a purely “cyber” risk analysis, side-channel risk assessment represents a genuine paradigm shift in system development. It no longer falls solely on developers, but on an entire production chain. Taking the example of a smartphone, it would be necessary to control potential leaks related to repeated touchscreen inputs, the presence of light that could reveal sensitive computations, data retention time in RAM, and so on.
To the best of our knowledge, side-channel attacks have never been exploited at large scale, and they continue to represent a mainly theoretical risk (as their exploitation context is extremely constrained)… although their cost can be very real. As mentioned, the Spectre and Meltdown attacks had tangible impacts in terms of costs, whether financial or computational.
Side-channel attacks are of course taken into account in established risk assessment methodologies (such as EBIOS from ANSSI or TEMPEST, which we previously mentioned). However, the associated likelihoods are often classified as low, and even so, the inherent variability of this type of attack makes it difficult to define sufficiently generic recommendations. Today, particularly for operations involving cryptographic keys, industry standards encourage constant-time execution, stronger separation between secret and non-secret data, and more frequent key rotation.
Illustration : LINC